3 WAYS TO REDUCE YOUR VETERINARY PRACTICE’S ONLINE RISK
As originally published for VetPartners.org
by Clint Latham, JD
Ask Jan Founding Expert
There is no denying that the web browser has become the new operating system. What does that mean in non-tech geek speak? For years, the cyber security world was focused on the computer operating system—primarily Microsoft Windows and Apple’s MAC OS X. Now, it’s focused on web browsers, like Chrome, Firefox, and Safari, because these browsers have become so powerful that they present a greater security risk to businesses and individuals.
With the rise in cloud-based practice management systems, veterinary practices now rely almost 100% on web browsers to access and manage their data. From a technology management perspective, this is great. Cloud-based practice management systems reduce our dependency on our local hardware. But, cloud-based also means we increase our web presence and exposure to growing cyber security threats. Let’s look at some numbers:
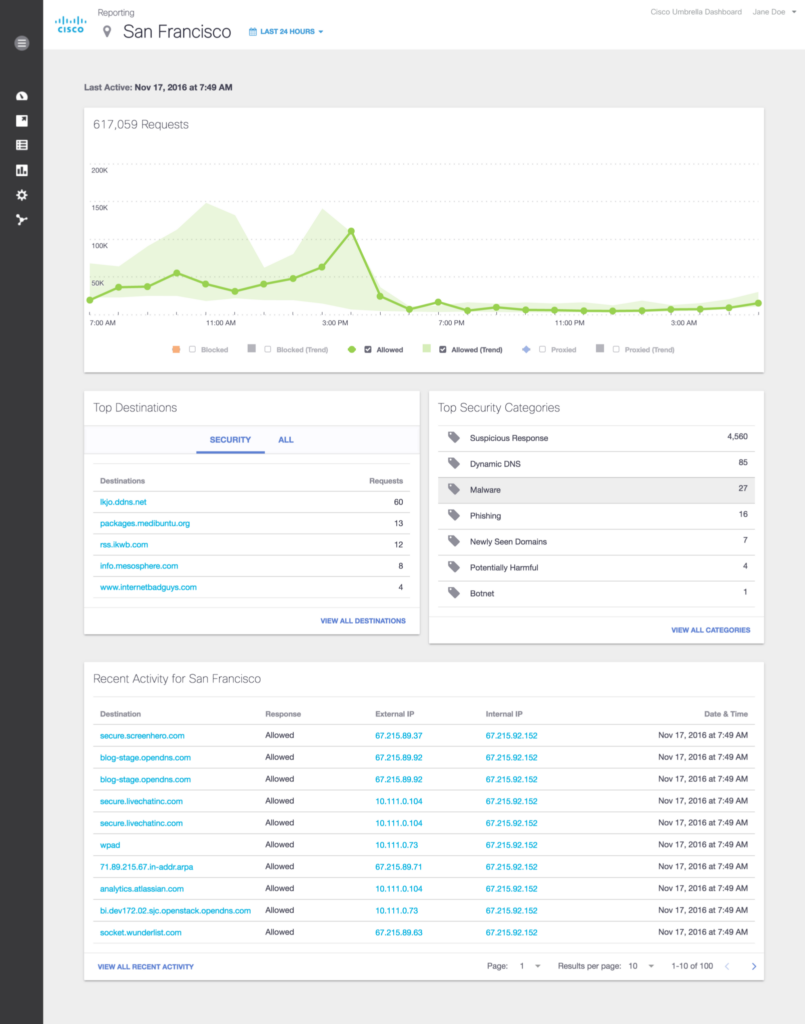
This report comes from a web protection tool used to protect Lucca’s clients. As you can see, this practice averages 617,059 web requests per day. If you use a local practice management software, like Cornerstone, Avimark, or Infinity, you can cut that number down to 308,529 web requests per day. In this 24-hour period (pre-COVID), Lucca stopped 4,560 cyber security threats for this practice. At the start of COVID-19, Lucca saw a 30% rise in cyber security threats, and they continue to rise today, putting your practice’s data at increased risk.
Here are three steps you can take today to help protect your data.
1: CREATE UNIQUE, STRONG PASSWORDS, AND STORE THEM IN A PASSWORD MANAGER
Most practices get hacked because they have guessable or previously compromised passwords. How many of you use Idex**** as your login to Cornerstone? Or, when creating a password that requires one capital letter, one number, and one symbol, do you capitalize the first letter, and add the number 1 and an exclamation point to the end?
Passwords like Welcome1! are the most commonly hacked—it’s any hacker’s dream. By using social engineering or a single crafty email, they will be able to get your password. To make matters worse, your password then gets added to black-market lists. This allows hackers to automate the hacking process with little to no effort.
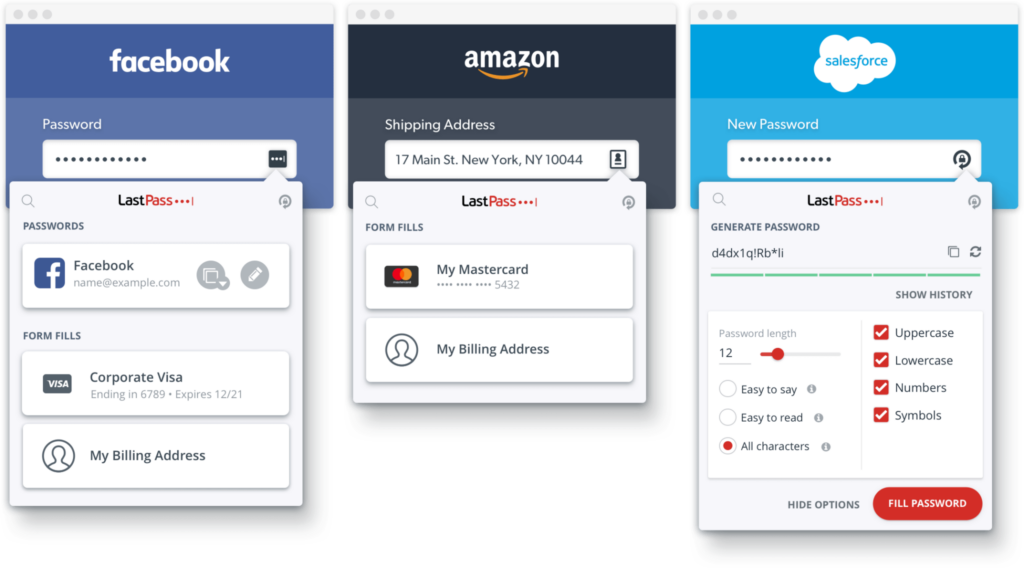
Implement a password manager, like 1Password or Lastpass. Using a password manager to create and manage your passwords is the first step to better internet security.
2: KEEP YOUR SOFTWARE UPDATED
The easiest step you can take, and the one that makes the biggest impact, is to keep your operating system, web browser, and software up to date. This includes all PC’s, laptops, tablets, and smart devices. These updates include important security changes that help to keep you safe. Hackers only need to find one-way in, while we are faced with the challenge of finding all possible entry points.
Schedule your updates to minimize the impact on your practice—there’s nothing worse than being in the middle of a client transaction when Windows decides it’s going to shut down and install updates.
3: ENABLE TWO-FACTOR AUTHENTICATION ON ALL CRITICAL ACCOUNTS
For any mission-critical accounts, including email, banking, and Quickbooks, you should enable two-factor authentication. When you sign in to one of these accounts, you have to enter a unique one-time code. This code can be generated through an app, like Authy, or a simple text message that’s sent to your phone.
Once, two-factor authentication saved me. While traveling to a practice, I did what most people do. When I got to the airport, I opened up my laptop to check my email. I had been working on some HIPAA compliancy issues for a colleague in human medicine, and I received an email from the HIPAA auditor that looked legitimate. The email indicated he needed to share a confidential document. To access the document, I needed to log in to Microsoft Sharepoint.
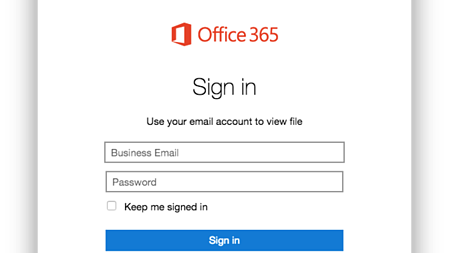
This was a legitimate process, and something we would do frequently. However, there was something that gave it away as a scam. When I logged into this fake Microsoft Sharepoint account, I wasn’t prompted to enter my two-factor authentication code. (I had previously enabled two-factor authentication on my business email account.) I was then redirected to a legitimate government form about HIPAA. I thought it was weird that he would password-protect this document, and was going to contact him to find out why. Then it happened—I started getting two-factor authentication requests for my email account. Someone was trying to log in to my account from Pakistan. Because I had enabled two-factor authentication, they weren’t able to access it. I then used my password manager to create and update a new complicated password, and moved on.
Had I not enabled two-factor authentication on my email account, I would have been scammed. They would have had complete access to my account, and could have caused some serious damage. Even those of us who think about cyber security everyday run the risk of being caught off guard. The best way to protect ourselves is to have tools in place that can cover our tracks.
Following these three simple steps, and turning them into habits, will help you become one of the safest practices on the internet.
About Clint

With two senior Yorkies, Clint (CJ) understands the need to have a trusted veterinarian to care for his family members. Clint’s goal is to help uncover the mystery of data security for DVM’s across the country so they can focus on what is most important: quality care for our furry friends. While working and speaking with practices all across the country, Clint saw that there were a number of practices that have a great local IT guy who needs the security and data insights specific to the veterinary industry. In an effort to find a way to support independent IT professionals while simultaneously providing security and data insights to those who protect our animal companions, Clint founded Lucca Veterinary Data Security.